SonicOS Version
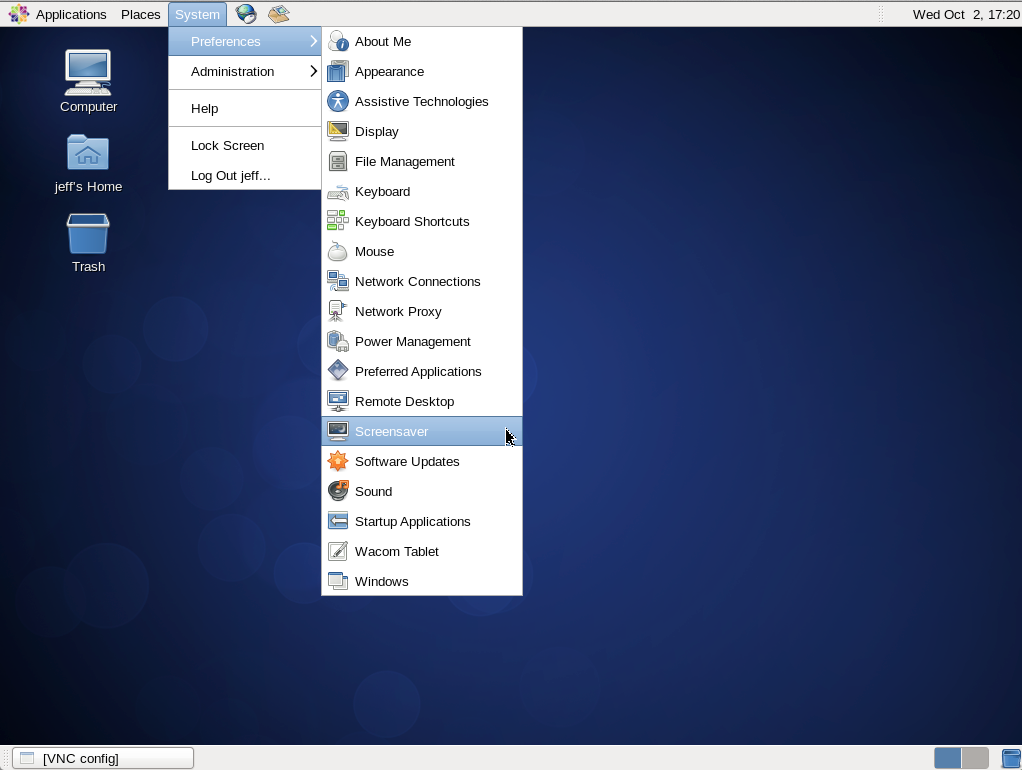
There are several great tutorials out there on how to setup a SonicWall SSLVPN. Each one is somewhat different as the SonicOS changes and the steps and location of items changes from release to release. So, while they are all similar, this tutorial was done using a SonicWall NSA 3500 running SonicOS Enhanced 5.9.0.0-91o. And since verions 5.8.1.13 is recent in my memory, I have notes for that version here too. You will see just between these two releases (5.8.1.13 and 5.9.0.0) there are a few differences.
Create a SonicWall SSLVPN Setup Tasks
There are 3 basic tasks to create a SonicWall SSLVPN.
- Create the SSLVPN. This includes setting up proper routes.
- Create your users and give them proper access to the right devices on your network.
- Install the NetExtender SSLVPN clients
Step 1 – Create the SSLVPN
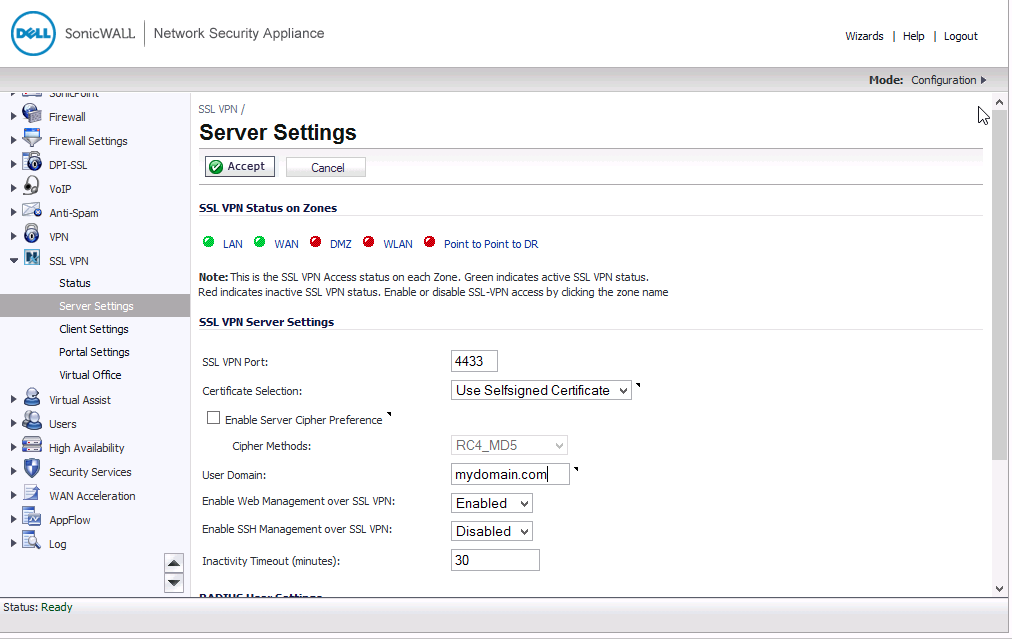
Login and browse to the SSL VPN / Server Settings page. Populate the form like I did below. Don’t forget to to do the following:
- Be certain that the WAN interface is clicked so that it is green. No reason to have a VPN setup if you can’t connect to it from the WAN. I also turn on LAN so that I can test it internally.
- Choose a port. I always the default 4433.
- If you need to use a signed certificate go to system / certificates and manage that there.
- Tell it the domain that you want to use. The only thing that this matches to is the domain name that they will need to enter on the NetExtender client side.
- If you need to manage this SonicWall over this VPN directly you will want to Enable Web Management and likewise if you use SSH for SonicWall management, turn that on too.
- The Inactivity Timeout will disconnect clients if they are inactive longer than this time period.
- Setup the Radius settings if you use Radius. I am not for my VPN, so I ignored that.
- Setup the URL for downloading the NetExtender clients if you wish to enable the client to download them from a site that you completely control. This has been good for me because sometimes there are specific versions of the NetExtender client that I want my clients using due to bugs or other.
Next, we go into SSL VPN / Client Settings.
This is where things are a bit different between 5.8 and 5.9. In SonicOS 5.8.1.13, one configures the whole DHCP setup completely in this area by setting the interface where the addresses are routed that you want to use–like X0 for example, Then setup the range using the start ip and end ip and then all of the other network stuff that you would normally expect such as WINS if needed, DNS, etc… You would then to to SSL VPN / Client Routes to set that up like we will describe later for 5.9.
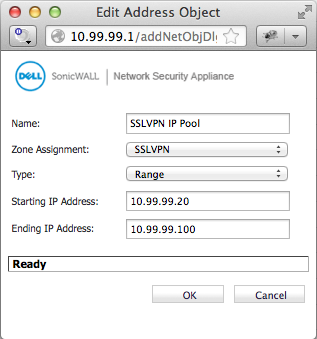
In SonicOS 5.9.0.0, it appears that they are adding a feature to allow you to have more than one profile. Hopefully that comes in a new release. At the moment, you edit the Default Device Profile. On the Settings tab, you currently only can setup the SSLVPN IP Pool that you define in the Network / Address Objects page.
To the right is how I defined my SSLVPN DHCP pool Network Object on my 5.9 SonicOS.
This is different than the 5.8.1.13 SonicOS and therefore, give you more flexibility as it doesn’t have to draw addresses from a current network that you have assigned to an interface.
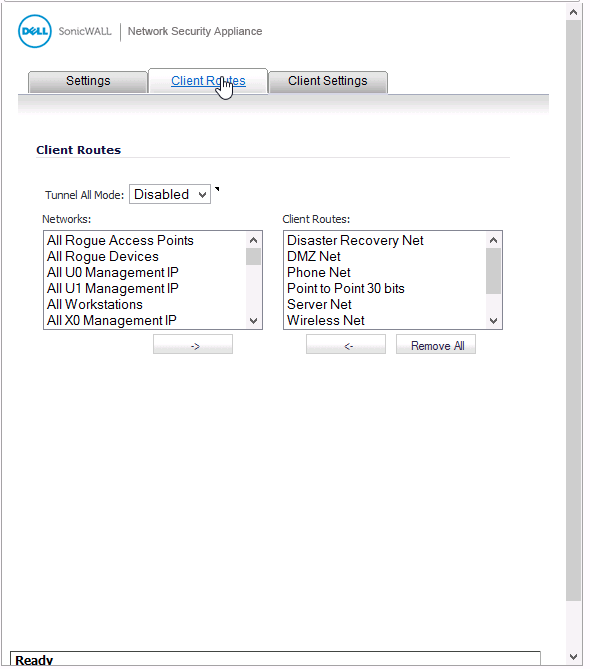 On the Client routes tab you need to choose from the address objects defined in Network / Address Objects which ones you want to allow the clients to connect to. In SonicOS 5.8.1.13, this is defined in SSL VPN / Client Routes. In the example to the right, you see that I have added a list of routes for the clients to use through the NetExtender client when they connect. Note that these routes are the superset of the routes that you want people to be able to connect to. Later on as we configure users, you can specify specific routes for individual users.
On the Client routes tab you need to choose from the address objects defined in Network / Address Objects which ones you want to allow the clients to connect to. In SonicOS 5.8.1.13, this is defined in SSL VPN / Client Routes. In the example to the right, you see that I have added a list of routes for the clients to use through the NetExtender client when they connect. Note that these routes are the superset of the routes that you want people to be able to connect to. Later on as we configure users, you can specify specific routes for individual users.
Finally, in SonicOS 5.9.0.0 you need to go to the Client Settings tab to setup your WINS, DNS, etc… for the client to use. In 5.8.1.13, you will have already done this.
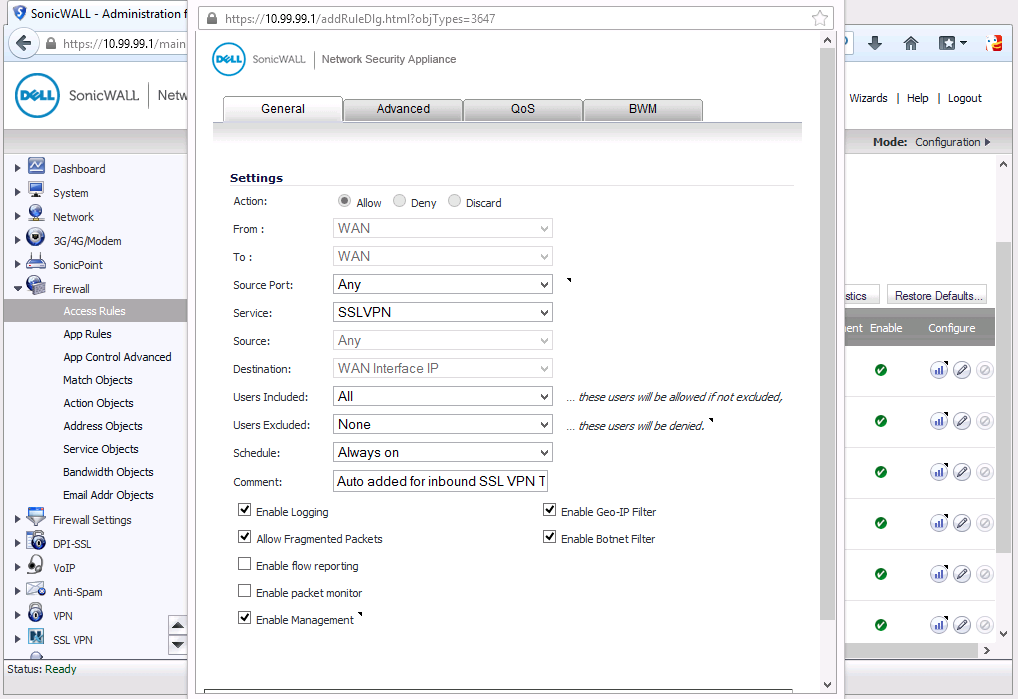
Finally, you will want to go into your Firewall settings and be certain that a rule was automatically created on your WAN interface to allow SSLVPN connections. If not, add one as shown below:
I should also mention that there is also a Portal Settings page where you can setup a portal for your users to browse to, download their client, etc… As this option is cool, but unnecessary to getting it working, I have left that out for a potential tutorial later on someday.
Step 2 – Create the Users
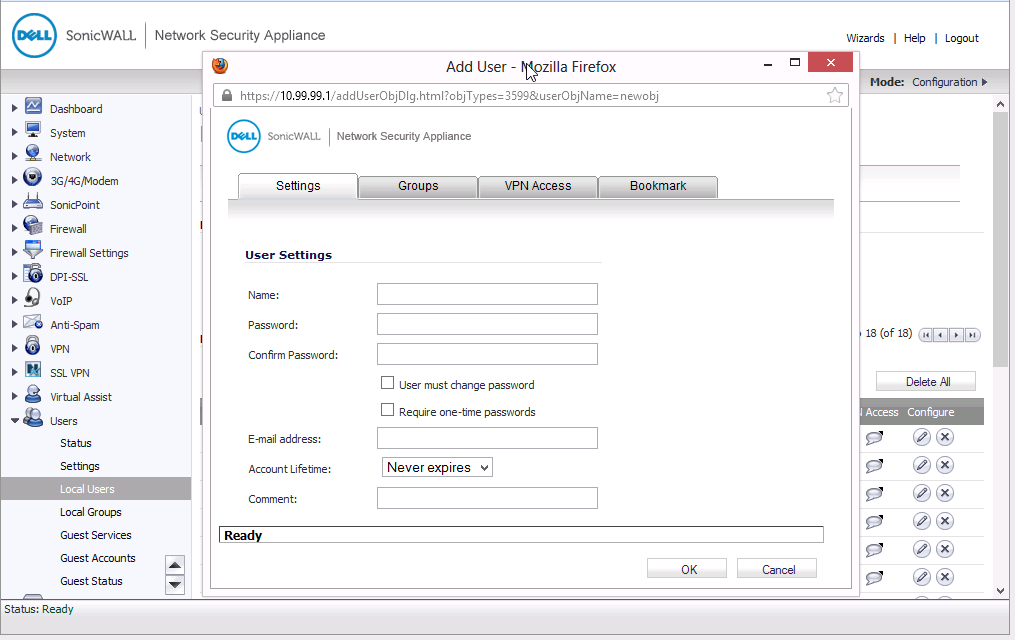
Navigate to Users / Local Users and then click the button to “Add User”. This will give you the screen below:
Populate the fields:
- Name – This is actually the username, this is what they will use to login with using the NetExtender client.
- Password / Confirm Password – Obviously type in the password for the user in both of these fields.
- Check Boxes – You can force them to change their password or make their password expire after each use if desired.
- Email address – Enter their email address.
- Account Lifetime – Set to Never Expire if you do not know how long the user will need this account, or set it to the proper timeframe if known.
- Comment – This is where I typically put the user’s actual name as the name field is for their login. I also put other comments to remind me why this user has access, if it is a vendor, who in the company they are reporting to, etc…
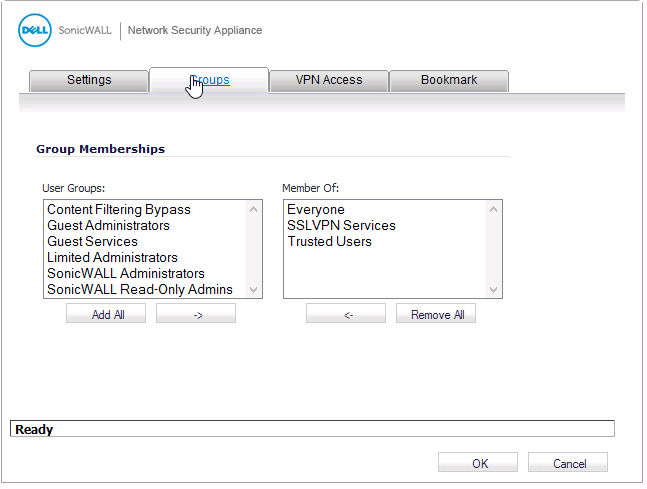
Groups Tab
On the groups tab be sure to give the user access to the SSLVPN Services Group membership as shown in the example below:
There are two more tabs that we won’t display but will discuss:
- VPN Access – This is where you specify the exact routes that you want the client to be able to use when they connect to the NetExtender VPN. This gives you complete control over which machines they can connect directly to. But remember, once you give access to an outside individual to a machine inside your network, they now have access to anything that machine has access to.
- Bookmark – This allows you to define shortcuts for directly connecting to Terminal Services, VNC, Telnet or SSH. We may cover this in a separate post someday.
With that, you should be done configuring your user for SSLVPN access.
Step 3 – Install and Configure the SSLVPN NetExtender Client
This requires that you have registered your SonicWall and have setup your access to their support portal at https://www.mysonicwall.com/Login.aspx. You will then login to their support site and download the NetExtender clients that your users will need: Mac, Windows, Linux, etc…
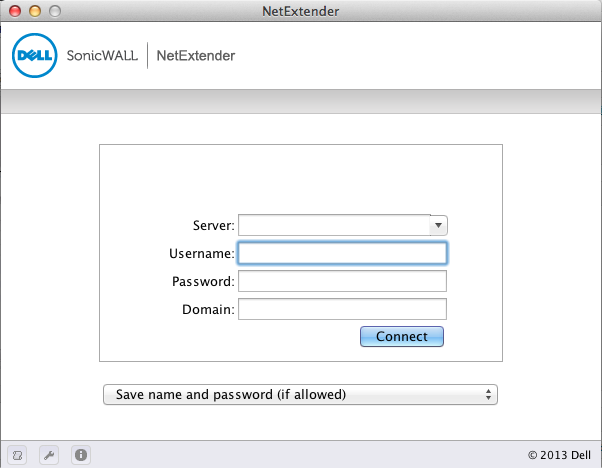
Once the NetExtender client is installed and launched, you connect by entering the either the IPADDRESS:Port or if you have setup DNS, the FQDN:port for your sonicwall’s WAN interface. For example: x.y.q.z:4433 or sslvpn.mydomain.com:4433.
The user will enter their username and password defined in step 2 above and the Domain as defined in Step 1 above and then connect.
Once connected, there are 3 tabs in your
NetExtender client:
- Status – Allows you to see how long you have been connected, etc…
- Routes – Shows you the routes that are being routed through the SSLVPN client. This is great for troubleshooting why you can’t get places.
- DNS – shows you the DNS servers and their priority for your client.
That should be it. Choose the Disconnect button when you are done and you will be disconnected.
Latest posts by Jeff Staten (see all)
- Configure Your HP Procurve Switch with SNTP - May 5, 2015
- Configuring HP Procurve 2920 Switches - May 1, 2015
- Troubleshooting Sendmail - November 28, 2014
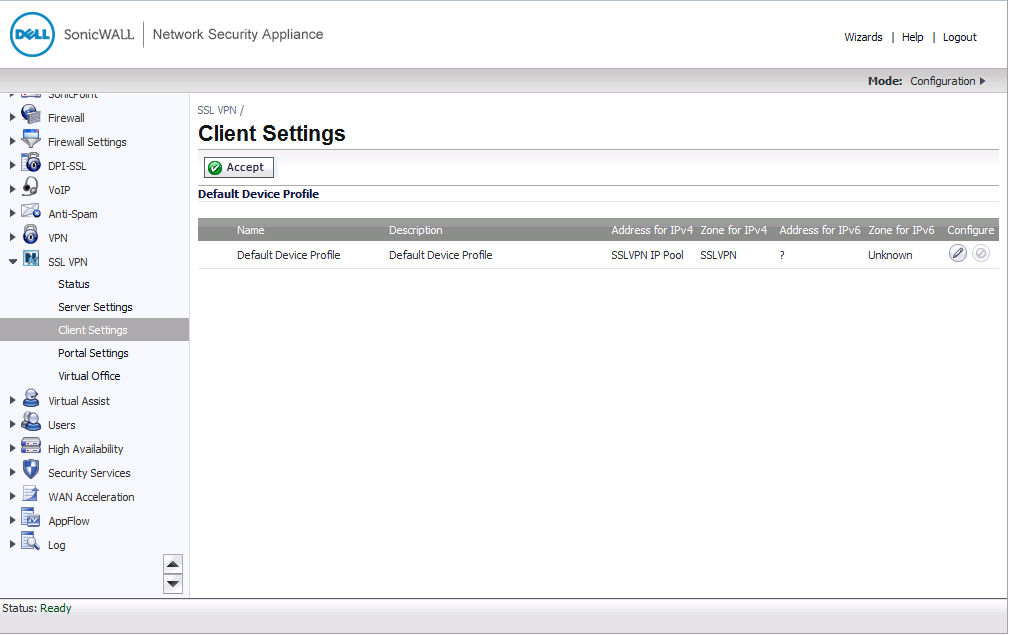



In SonicOS 5.9.0.0, it appears that they are adding a feature to allow you to have more than one profile. Hopefully that comes in a new release. At the moment, you edit the Default Device Profile. On the Settings tab, you currently only can setup the SSLVPN IP Pool that you define in the Network / Address Objects page.
Post a screenshot because all I get is “Address Object does not match SSLVPN zone”
IT Guy, Thanks for the suggestion. I have added the screenshot as requested with the Caption: Create Your SSLVPN DHCP POOL Address Object. Hopefully that helps you out.
Hi Jeff,
I have a VPN tunnel between us and site B, My SSLVPN only sees the local LAN and cannot see the servers on site B. They are on different subnets BUT when we are here in the office we CAN see and ping the servers in site B. We have a NSA3500. Any suggestions? My initial thought was under USERS|Local Groups, SSLVPN Services – VPN tab and add the site B network to the access list along with X0 subnet (which already installed) – would this be correct? Anything else I need to do or am I on the wrong track?
Thank you.
This sounds an awful lot like you need to work with your client routes and on your VPN access tabs. These specify the objects and routes that your SSLVPN users can utilize when connected.
For client routes, go to: SSL VPN / Client Settings / Configure Button / Client Routes Tab. Be sure to add one for the address space on the other side.
For VPN Access, go to users / local users, then edit the user that can’t connect. Go to the VPN Access tab and verify that the user can get to the places you want by adding the networks to the access list for that user.
Give that a try.
I am having the same problem, my clients cannot browse the computers or servers on the remote site. I suspect that the problem is the difference between the 5.8 and 5.9 firmware, specifically the lack of a “NetBIOS over TCP/IP’ option to enable. The 5.9 firmware doesn’t have it anywhere and I have tried several combinations of objects, rules, and NAT policies to route NetBIOS over the SSLVPN. Any specific suggestions?
Kevin,
Let’s take this one step at a time. It sounds like the problem you are having is that you cannot reach the servers using their Netbios hostnames. Let’s take a step back and see if you can reach them via their IPAddresses, then by FQDN in your DNS. If you can reach them through IP, then the problem is with Netbios. However, if you can’t reach them via IP either, the problem is likely due to client routes or the “VPN Access” tab of the user configuration.
SMB and DNS are working. I can reach server, shares, and workstations through either IP address or FDQN once connected. What I can’t do is go to Network and see workstations, servers, or resources advertised from the remote domain on my local domain while connected to SSL VPN.
Again, the one thing that is different between 5.8 and 5.9 firmware for SSL VPN is the lack of a NetBIOS of TCP/IP enable or disable option. It used to be in Client Settings I believe but shows up nowhere in the new Users or SSL VPN configuration options.
I have a TZ210 with 5.8 firmware and a TZ215 with 5.9 firmware. Each is setup exactly the same as the other with one difference. The 5.8 has the NetBIOS over TCP/IP option enabled, the 5.9 doesn’t have the option anymore. I can see remote resources while browsing on the local domain when I setup the TZ210 and I can’t with the TZ215 (everything else works on both routers). I guess my question is this: Is their a combination of firewall rules, objects, and NAT policies (and SSL VPN access groups) that can replicate the same functionality as the NetBIOS over TCP/IP option from the old firmware on the new 5.9 firmware?
Kevin,
Thanks for the clarification. I now see your point. What is clearly in 5.8, is not there in my 5.9 version. My 5.9 SW’s are at 5.9.0.3-117o-HF139012-3o. I have seen features disappear and then come back in a future release. For your sake, I hope that this one does too.
Jeff
Hello and there is another issue using the SSLVPN net extender software. The client doesn’t automatically disconnect even though you tell it to. Where can you change the setting that says “unlimited” to a certain amount of time in the firewall SSL VPN Client or server settings. I changed the connections settings from destination IP and source IP to 128. Anything else I am missing? Sonic wall said to go back a firmware version, then the next engineer said to go to the latest. I have net extender version 7.3.x.
David,
I think that you are looking for the “inactivity timeout” that you can find on the SSL VPN / Server Settings page.
Jeff
My wife’s company uses this software (not what I would recommend) but they issue a client IP of 192.168.99.xxx and she can connect to SMTP traffic via Outlook and instant messaging. However she is unable to connect to the internet and get any port 80 traffic. When I look at what is being fully issued by her company’s VPN server, there is no gateway! Then when I look in the VPN client settings under the ‘Routes’ tab, the only entry is 192.168.1.0! The lonely IT admin is telling me that I have change my entire home network either to 192.168.1.0 or completely off of the 192.168.0/24 subnet! When I have her disconnect from her company’s VPN obviously she can connect to our home network still AND get out on the internet with no issues. Am I losing my mind or should he simply had the 192.168.99.0 route to the list of available routes to allow her client to access port 80 traffic!?
Thanks! -Chris
Chris,
I suspect that what is happening is that her company is using the same address space in the office as you are at home. Typical home networks are using 192.168.0.0/16 while company networks are using 10.0.0.0/8 or 172.16.0.0/12. If this is the case, what the company is doing is completely fine, but will have lots of conflicts with home networks.
Seems like there are only 2 ways to go about resolving this as I doubt the company will re-address its network. 1-Readdress your home network, or 2-have her tether onto her phone and then connect to the VPN. If she will be connecting a lot to the VPN, likely option #1 is all that you can do as you will likely exceed your mobile plan’s limits.
Jeff