Most IT Network Administrators are tasked with putting a content filter into place to resolve a myriad of HR issues. Several years ago, I selected a SonicWall NSA to do this for my organization because it did a good job with VPN, Firewall, and UTM in addition to content filtering. One thing that I have noticed with SonicWall is that whenever you think you know exactly how to do something, upgrade and you’ll have to figure it out again. This article gives a pretty good description of how to configure SonicWall Content Filtering on SonicOS version 5.9.0.0. If you are using a different version, I suspect that at a minimum the general steps in this article will help you along. This article also assumes that you have purchased the SonicWall Content Filtering option with your device.
Configure SonicWall Content Filtering – Step 1
The first step in configuring the SonicWall content filtering service (CFS)
is to navigate to the section in the SonicOS menu. Just navigate down into the “Security Services” area and find the Content Filter option. This will drop you into the Content Filter page. Once here, you will want to find the
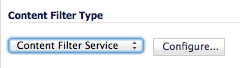
Content Filter Type area. Choose “Content Filter Service” then hit the Configure Button. This will then take you to the SonicWall Filter Properties page which has 4 tabs. We should be on the CFS tab. Here, we would likely want to check the “Enable HTTPS Content Filtering” and “Block Access to URL” options. You should also probably think over the behavior that you want the SonicWall device to perform if somehow it cannot reach the SonicWall CFS services.
In my case, I chose to “Allow traffic to all Web sites” because I didn’t want the unavailability of SonicWall’s CFS services to shutdown my zones protected by CFS services.
Define SonicWall CFS Policy
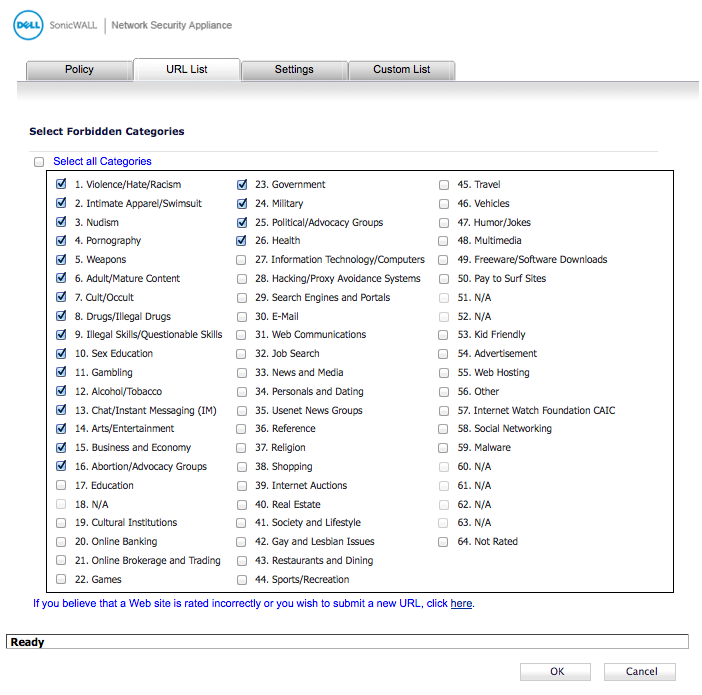
We now switch to the “Policy” tab to begin configuring the specific policy. If we don’t have a policy defined yet to modify, we hit the “add” button. Otherwise, we choose the pencil button next to the policy that we need to edit. The first page will allow us to name our policy, the On the Policy tab, we select the URL List tab.
The URL List tab is where we choose which categories we wish to block on this specific policy.
The example above shows a typical “Forbidden Categories” section in the SonicWall Content Filtering Service definition. Once we have selected the appropriate categories for our organizations, we go to the “Settings” tab.
Exceptions to SonicWall Content Filter Policies
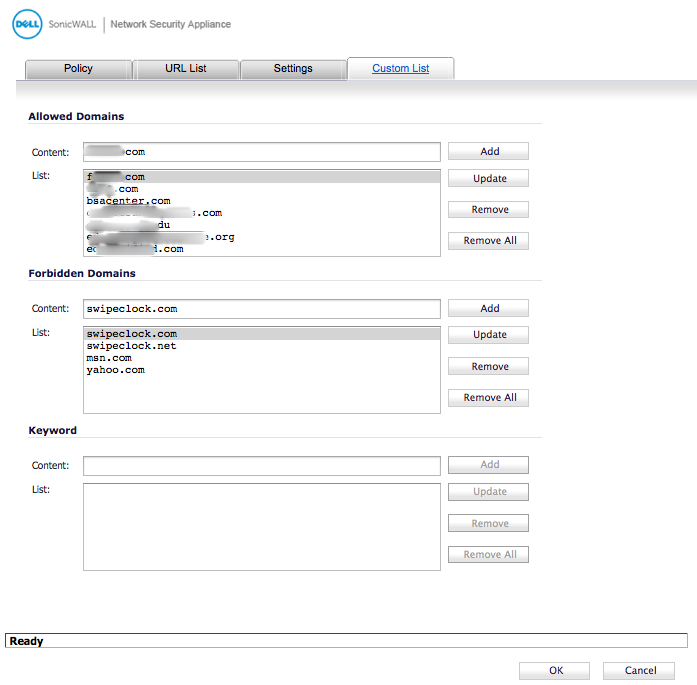
The most important part of this page is the custom list settings. You may want to add exceptions to the policy. This Settings tab is where you decide if the exceptions will be set globally or per policy. In the screen below, we can choose to have our Allowed Domains (whitelist) and our Forbidden Domains (blacklist) on either a per policy or a global basis.
One final feature that the Settings page gives you is the ability to specify the time of day that the filter will be used. This gives you the opportunity to allow different browsing habits for off-hours vs work hours, etc…
Next comes the “Custom List” tab. If we choose the per policy option on the settings tab, then this is where we add our white listed/black listed domains. You can see the domains listed below under the Allowed and Forbidden domain sections. Sorry for the blotches in the image. I had to purify my image before I could post it here.
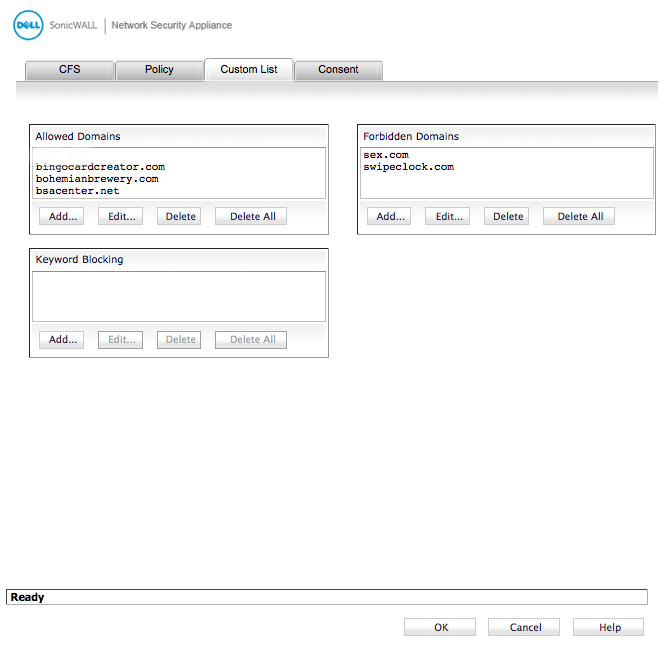
If we chose the Global allow and forbidden list on the settings page, then we edit the global list on the CFS page / Custom List which will define the policy for all policies that are configured for global allowed / forbidden domain listings.
Apply the Content Filter Policy to a Zone
Finally, once we get the SonicWall Content Filter Services Policy configured, we need to put it in place so that it is used. We apply a policy in SonicWall to a specific zone. We choose the zone by going to the Network area of the main SonicOS menu, and choosing “zones”. This will display all of the zones configured in our SonicWall device. We will then choose the zone to apply our policy to. In my case, I chose the “LAN” zone as shown below.
we need to put it in place so that it is used. We apply a policy in SonicWall to a specific zone. We choose the zone by going to the Network area of the main SonicOS menu, and choosing “zones”. This will display all of the zones configured in our SonicWall device. We will then choose the zone to apply our policy to. In my case, I chose the “LAN” zone as shown below.
Clicking on the Pencil button for our zone allows us to change the properties of the zone, including the Content Filter Services policy that we want to put on the zone.
First, we select the check box to Enforce Content Filtering Services.
Then, we select our CFS policy from the listing.
Putting the SonicWall CFS Policy in Place
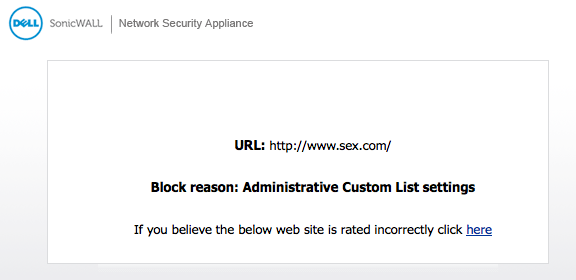
When we hit the OK button, it applies our SonicWall Content Services Filtering policy to the zone. With our policy in place, workstations and other systems protected by the CFS policy will then be blocked from sites in the categories we chose. Browsers that attempt to contact web pages blocked by the policy will receive a screen similar to the image below.
Any you find web pages or other destinations being blocked that you think should not be, you can simply add their domains to the appropriate allowed / forbidden list as mentioned above.
Latest posts by Jeff Staten (see all)
- Configure Your HP Procurve Switch with SNTP - May 5, 2015
- Configuring HP Procurve 2920 Switches - May 1, 2015
- Troubleshooting Sendmail - November 28, 2014





Hello, I need to know what is meant by “per policy” and “global” with respect to custom list settings of CFS policy. Also, I noted that there are custom settings like “always on”; “work hours”; “flexiblock”; “weekend hours” under “Filter Forbidden URLs by time of day”. Kindly define these custom settings that covers a certain hours per day. I await your response. Thank you.
Victor A,
You can have multiple Content Filtering policies defined that you can apply to different zones in your SonicWall configuration. You can then have exceptions that you would list. This list of exceptions can be done globally for all policies or for just a specific policy. That is the difference between global and per policy.
As for the schedules you listed. They are defined in your SonicWall under System / Schedules which allow you to define the schedule that your policy will be enforced on a per policy basis.
We are going to be replacing our existing Cisco 5505 firewalls in our two offices with Sonicwall TZ-215 units. While we can do most of the configuration ourselves, it would be very helpful to have a consultant to call on as needed for setup help, advice on best practices, etc. Do you have anyone that you could recommend (individual or a company) that could provide this service for us?
Thanks! I appreciate your articles and have found them to be very helpful.
Thanks Steve.
I am glad that you appreciate my articles.
While I don’t know about any SonicWall consultants in your area, I would be happy to help field whatever questions you may have.
Jeff
Thanks – just the info I was looking for! Nice pics and instructions.